Enhancing Security and Efficiency with Access Control Programs
Access Control Programs have become an essential component of security management in today’s business environment. As organizations increasingly rely on technology and digital services, the need for robust security measures has never been more critical.
Understanding Access Control Programs
An access control program is a systematic approach to managing and restricting access to resources within an organization. This includes premises, data, systems, and sensitive information. Effective access control systems not only secure physical locations but also protect valuable digital assets against unauthorized access, thereby enhancing overall operational efficiency.
The Importance of Access Control in Telecommunications
The telecommunications sector is particularly vulnerable to security threats due to the vast amounts of data handled on a daily basis. Access control programs are vital in mitigating risks associated with data breaches and unauthorized access. Here are several reasons why access control is significant in telecommunications:
- Data Protection: Telecommunications companies handle sensitive customer information. Effective access controls ensure that only authorized personnel have access to this data.
- Regulatory Compliance: Many sectors, including telecommunications, are subject to stringent regulations that require robust data protection measures. An effective access control program can help in achieving compliance.
- Operational Efficiency: By implementing a well-defined access control strategy, companies can improve operational workflows, reducing bottlenecks associated with security clearance processes.
- Risk Management: Access control programs play a crucial role in identifying and mitigating risks, thus preserving the integrity of the telecommunications network.
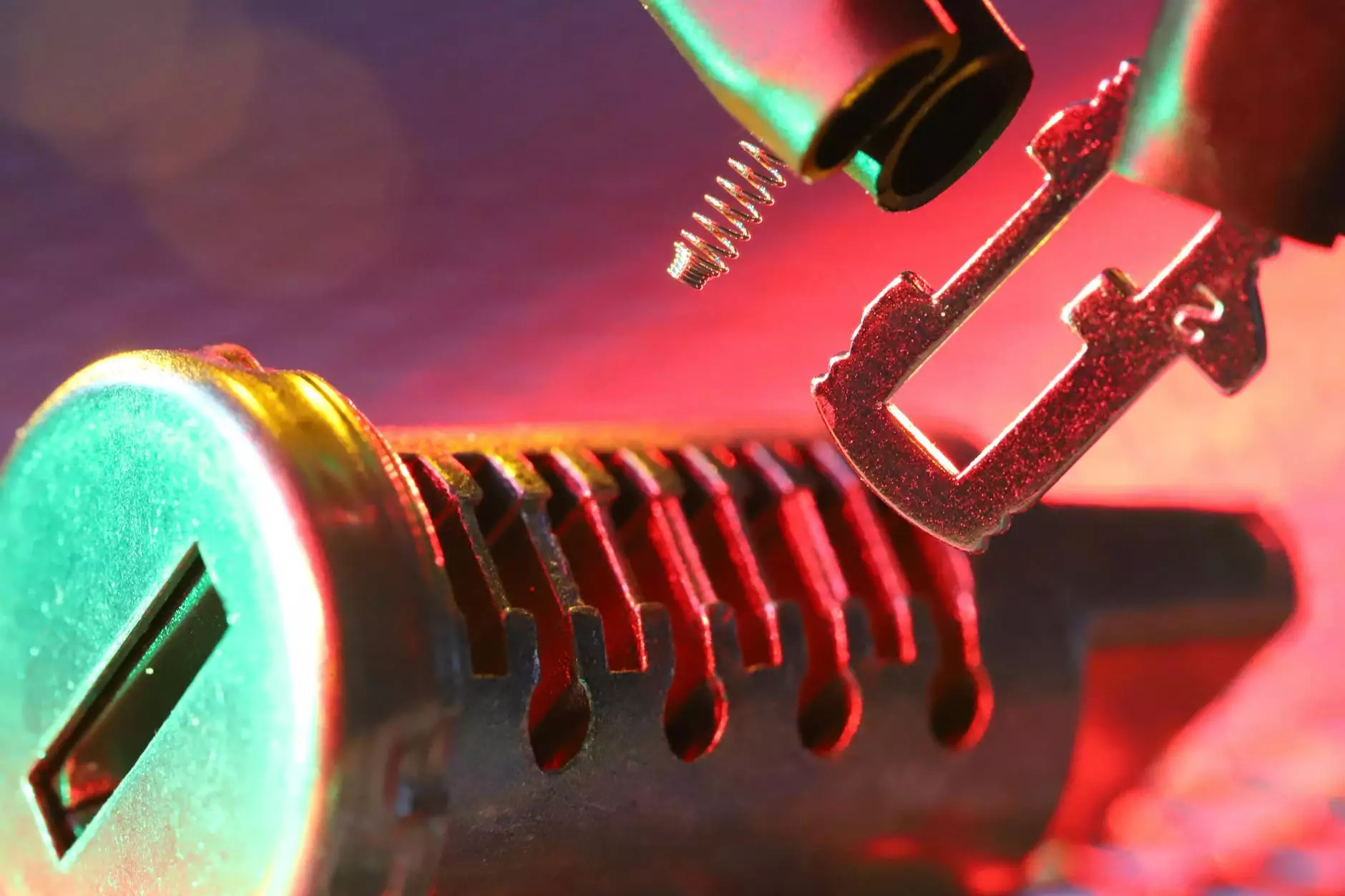
Types of Access Control
Access control systems can be categorized based on their implementation methods and authentication processes. Understanding these types will help businesses choose the right program for their needs.
1. Discretionary Access Control (DAC)
In discretionary access control, the owner of the resource decides who has access. While this provides flexibility, it can lead to security risks if not managed carefully.
2. Mandatory Access Control (MAC)
Mandatory access control is more stringent and typically used in environments requiring high-level security, such as government and military installations. In MAC, access rights are regulated by a central authority based on multiple user attributes.
3. Role-Based Access Control (RBAC)
Role-Based Access Control assigns permissions based on the user's role within the organization. This method simplifies permission management and is scalable as organizations grow.
Implementing an Access Control Program
To efficiently implement an access control program, businesses should follow a structured approach that includes the following steps:
1. Assess Needs and Risks
The first step is to evaluate the specific needs of the organization along with the potential security risks. This assessment should cover all aspects of both physical security and data security.
2. Develop Policies and Procedures
Based on the assessment, organizations should craft comprehensive policies that define who has access to what resources, under which circumstances, and what processes are in place to monitor and review access.
3. Choose the Right Technology
Selecting the appropriate technology is crucial for the effective deployment of an access control program. Many companies offer advanced solutions incorporating biometrics, smart cards, and mobile access systems that can enhance security.
4. Training and Awareness
Employee training programs should be established to create awareness about the importance of access control and the role each team member plays in maintaining security protocols.
Benefits of Access Control Programs
Investing in a robust access control program brings a multitude of benefits, including:
- Improved Security: With comprehensive access controls in place, the risk of unauthorized access is dramatically reduced.
- Enhanced Monitoring: Access control systems provide logs and reports, facilitating monitoring of attempts to access restricted areas or data.
- Increased Accountability: By assigning specific access rights to individuals, organizations can hold employees accountable for actions taken under their credentials.
- Efficient Audit Trails: Access records can be used for auditing purposes, enabling companies to maintain compliance and track user activity effectively.
Challenges in Access Control Implementation
Despite the clear benefits, organizations may encounter challenges when establishing an access control program. Below are some common issues:
1. Resistance to Change
Implementing new access protocols may meet resistance from staff accustomed to previous systems. Clear communication about the benefits of the new system is essential in overcoming this challenge.
2. Cost Concerns
Depending on the scale of the organization and the technology chosen, costs can be prohibitive. However, the investment in security can yield substantial long-term savings by preventing data breaches and ensuring compliance.
3. Complexity of Management
As access controls increase, managing them can become complex. Businesses should consider integrated solutions that simplify this process.
Future Trends in Access Control Programs
As technology evolves, so too does the landscape of access control. Here are some trends shaping the future of access control programs:
1. Integration of AI and Machine Learning
AI and machine learning are increasingly being integrated into access control systems, allowing for advanced threat detection and predictive analytics to preempt potential breaches.
2. Cloud-Based Solutions
Cloud-based access control systems offer scalability and flexibility that on-premises solutions do not provide, allowing organizations to manage access remotely and efficiently.
3. Increased Use of Biometrics
With advancements in biometric technology, methods such as facial recognition, fingerprint scanning, and iris recognition are becoming standard in access control programs, providing enhanced security.
Conclusion
In conclusion, an access control program is an integral part of risk management that enhances security and operational efficiency within telecommunications and IT services. By understanding the various types of access control systems, implementing a tailored approach, and keeping abreast of emerging trends, organizations can safeguard their assets against threats while ensuring compliance with regulations. Investing in effective access control not only protects the organization but also fosters a culture of security awareness among employees, paving the way for a secure and efficient operational future.